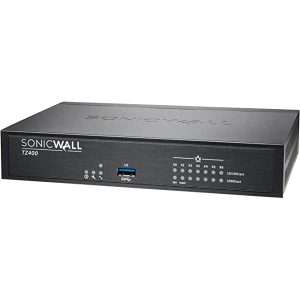
SonicWall TZ350 Network Security Appliance (Branded Used)
SonicWall TZ350 Network
- Firewall Throughput: Up to 1.5 Gbps
- Threat Prevention Throughput: Up to 600 Mbps
- VPN Throughput: Up to 1.1 Gbps
- Concurrent Connections: 150,000
- Maximum UTM/DPI Connections: 12,000
- Site-to-Site VPN Tunnels: 20
- SSL VPN Licenses (Maximum): 2 (25 with additional licenses)
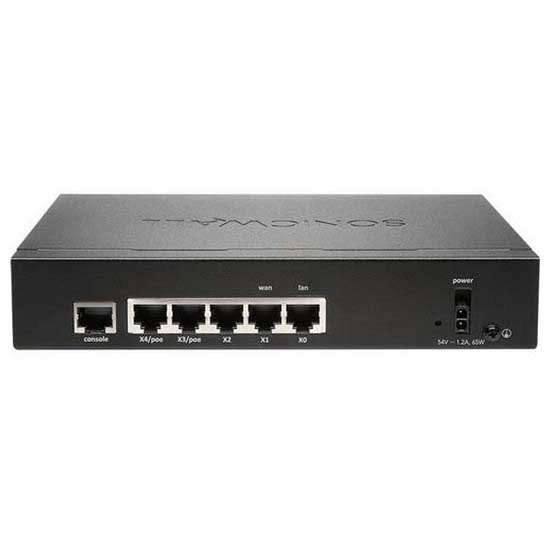
- Gigabit Ethernet Interfaces: 5 x 1 GbE (4 LAN, 1 WAN)
- USB Ports: 2 x USB 3.0
- Power over Ethernet (PoE) Ports: None
- Processor: Dual-core
- RAM: 1GB
- Storage: 8GB
10,000 ₨
Description
The SonicWall TZ350 is a comprehensive network security appliance that provides advanced threat protection and secure network connectivity. It is ideal for businesses looking to safeguard their networks from a wide range of cyber threats while ensuring efficient and reliable network performance. The TZ350 offers a combination of firewall, VPN, and security features to defend against modern cyberattacks.
Key Features:
-
- Firewall Protection: Provides state-of-the-art firewall capabilities to block unwanted incoming and outgoing traffic, safeguarding against intrusions and cyber threats.
- Intrusion Prevention System (IPS): Offers real-time protection against network attacks, identifying and blocking malicious traffic to prevent breaches.
- Gateway Anti-Virus: Scans incoming and outgoing traffic for viruses, malware, and other threats, ensuring that infected files do not enter the network.
- Content Filtering: Allows administrators to control internet access by filtering web content, blocking access to inappropriate or non-work-related websites.
- Secure VPN Connectivity: Supports Virtual Private Network (VPN) connections to establish secure and encrypted communication between remote offices and users.
- SSL Inspection: Provides the ability to inspect encrypted SSL/TLS traffic to detect and block threats hidden within encrypted communications. (SonicWall TZ350)
- High-Performance: Delivers fast and efficient security with gigabit Ethernet ports and hardware acceleration for VPN and other security services.
- Advanced Threat Protection: Includes SonicWall Capture Advanced Threat Protection (ATP) to identify and block zero-day threats and sophisticated malware.
- SonicOS Operating System: Runs on SonicOS, SonicWall’s proprietary operating system, offering a user-friendly interface for configuration and monitoring.
- Wireless Network Security: Supports wireless security standards like WPA2/WPA3 to secure wireless networks. (SonicWall TZ350)
- Network Segmentation: Allows for the creation of multiple network zones with varying levels of security to isolate critical resources and prevent lateral movement of threats.
- Cloud Management: Offers cloud-based management for remote administration and monitoring, making it easier to manage distributed networks.
- Logging and Reporting: Provides extensive logging and reporting capabilities for monitoring network activity and identifying security incidents.
| Weight | 1 kg |
|---|---|
| Dimensions | 30 × 15 × 5 mm |















There are no reviews yet.